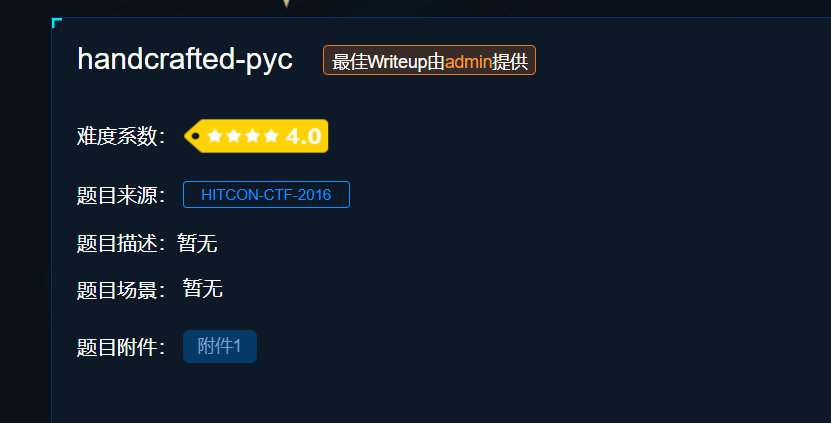
下载下来打开发现是python代码
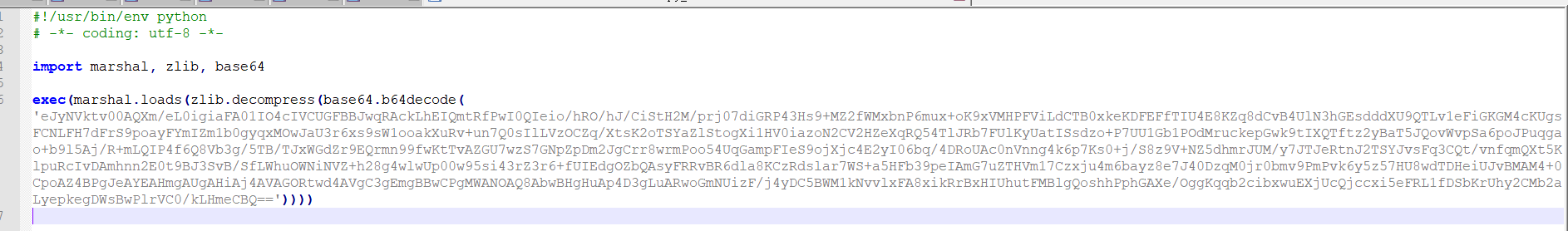
可以执行,但是看不到实际运行的代码,所以需要把实际的代码逆向出来,这个转换出来实际是object code ,object code和pyc文件只是相差一个文件头,补齐文件头尝试反编译
#!/usr/bin/env python
# -*- coding: utf-8 -*-
import zlib, base64
pyc = zlib.decompress(base64.b64decode(
'eJyNVktv00AQXm/eL0igiaFA01IO4cIVCUGFBBJwqRAckLhEIQmtRfPwI0QIeio/hRO/hJ/CiStH2M/prj07diGRP43Hs9+MZ2fWMxbnP6mux+oK9xVMHPFViLdCTB0xkeKDFEFfTIU4E8KZq8dCvB4UlN3hGEsdddXU9QTLv1eFiGKGM4cKUgsFCNLFH7dFrS9poayFYmIZm1b0gyqxMOwJaU3r6xs9sW1ooakXuRv+un7Q0sIlLVzOCZq/XtsK2oTSYaZlStogXi1HV0iazoN2CV2HZeXqRQ54TlJRb7FUlKyUatISsdzo+P7UU1Gb1POdMruckepGwk9tIXQTftz2yBaT5JQovWvpSa6poJPuqgao+b9l5Aj/R+mLQIP4f6Q8Vb3g/5TB/TJxWGdZr9EQrmn99fwKtTvAZGU7wzS7GNpZpDm2JgCrr8wrmPoo54UqGampFIeS9ojXjc4E2yI06bq/4DRoUAc0nVnng4k6p7Ks0+j/S8z9V+NZ5dhmrJUM/y7JTJeRtnJ2TSYJvsFq3CQt/vnfqmQXt5KlpuRcIvDAmhnn2E0t9BJ3SvB/SfLWhuOWNiNVZ+h28g4wlwUp00w95si43rZ3r6+fUIEdgOZbQAsyFRRvBR6dla8KCzRdslar7WS+a5HFb39peIAmG7uZTHVm17Czxju4m6bayz8e7J40DzqM0jr0bmv9PmPvk6y5z57HU8wdTDHeiUJvBMAM4+0CpoAZ4BPgJeAYEAHmgAUgAHiAj4AVAGORtwd4AVgC3gEmgBBwCPgMWANOAQ8AbwBHgHuAp4D3gLuARwoGmNUizF/j4yDC5BWM1kNvvlxFA8xikRrBxHIUhutFMBlgQoshhPphGAXe/OggKqqb2cibxwuEXjUcQjccxi5eFRL1fDSbKrUhy2CMb2aLyepkegDWsBwPlrVC0/kLHmeCBQ=='))
pyc_header = '\x03\xf3\x0d\x0a\x54\x85\x8e\x5e'
with open('code.pyc', 'wb') as wf:
wf.write(pyc_header)
wf.write(pyc)转换成pyc文件后,反编译一下
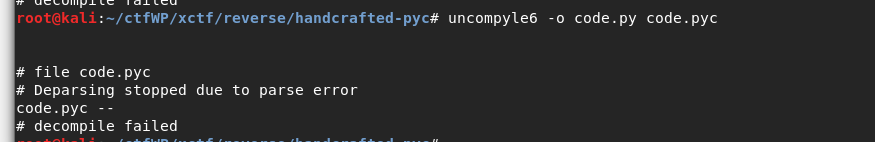
反编译失败,
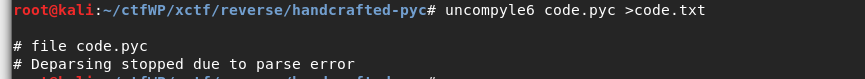
直接输入到txt文件中,看看汇编代码
# uncompyle6 version 3.6.5 # Python bytecode 2.7 (62211) # Decompiled from: Python 2.7.17 (default, Oct 19 2019, 23:36:22) # [GCC 9.2.1 20191008] # Embedded file name: <string> # Compiled at: 2020-04-08 22:15:48 def main--- This code section failed: --- L. 1 0 LOAD_GLOBAL 0 'chr' 3 LOAD_CONST 108 6 CALL_FUNCTION_1 1 None 9 LOAD_GLOBAL 0 'chr' 12 LOAD_CONST 108 15 CALL_FUNCTION_1 1 None 18 LOAD_GLOBAL 0 'chr' 21 LOAD_CONST 97 24 CALL_FUNCTION_1 1 None 27 LOAD_GLOBAL 0 'chr' 30 LOAD_CONST 67 33 CALL_FUNCTION_1 1 None 36 ROT_TWO 37 BINARY_ADD 38 ROT_TWO 39 BINARY_ADD 40 ROT_TWO 41 BINARY_ADD 42 LOAD_GLOBAL 0 'chr' 45 LOAD_CONST 32 48 CALL_FUNCTION_1 1 None 51 LOAD_GLOBAL 0 'chr' 54 LOAD_CONST 101 57 CALL_FUNCTION_1 1 None 60 LOAD_GLOBAL 0 'chr' 63 LOAD_CONST 109 66 CALL_FUNCTION_1 1 None 69 LOAD_GLOBAL 0 'chr' 72 LOAD_CONST 32 75 CALL_FUNCTION_1 1 None 78 ROT_TWO 79 BINARY_ADD 80 ROT_TWO 81 BINARY_ADD 82 ROT_TWO 83 BINARY_ADD 84 BINARY_ADD 85 LOAD_GLOBAL 0 'chr' 88 LOAD_CONST 121 91 CALL_FUNCTION_1 1 None 94 LOAD_GLOBAL 0 'chr' 97 LOAD_CONST 80 100 CALL_FUNCTION_1 1 None 103 LOAD_GLOBAL 0 'chr' 106 LOAD_CONST 32 109 CALL_FUNCTION_1 1 None 112 LOAD_GLOBAL 0 'chr' 115 LOAD_CONST 97 118 CALL_FUNCTION_1 1 None 121 ROT_TWO ... ...
2000多行,没贴全,LOAD_CONST 这一行有数字,看起来是可见字符,使用脚本跑出来,得到
with open('code.txt') as fp:
content = fp.readlines()
code = ''
for line in content:
if 'LOAD_CONST' in line:
pattern = re.compile(r'LOAD_CONST (\d*)')
result = pattern.findall(line)
if result[0] != '':
c = int(result[0])
code += chr(c)
print code
#llaC em yP aht notriv lauhcamni !eac Ini npreterP tohty ntybdocese!!!ctihN{noy woc uoc naipmoa eldnur yP nnohttyb doceni euoy rb ria}!napwssro :dorWp gnssadrow...elP esa yrtaga .ni oD tonurbf etecro)= .看起来是被打乱顺序了,第一个字符串应该是Call,通过观察发现
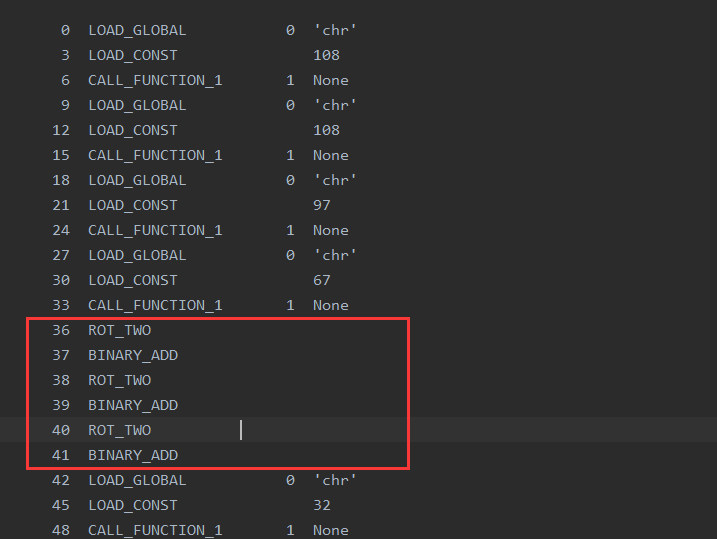
前四个字符串后面有三组 ROT_TWO BINARY_ADD ,感觉ROT_TWO可能是交换两个字符的位置,BINARY_ADD是位置+1,也就是这样一个流程,实际就是遇到ROT_TWO把前面的字符全部反转,然后写脚本
import re
with open('code.txt') as fp:
content = fp.readlines()
code = ''
for line in content:
if 'LOAD_CONST' in line:
pattern = re.compile(r'LOAD_CONST (\d*)')
result = pattern.findall(line)
if result[0] != '':
c = int(result[0])
code += chr(c)
print code
flag = ''
code = ''
for line in content:
if 'LOAD_CONST' in line:
pattern = re.compile(r'LOAD_CONST (\d*)')
result = pattern.findall(line)
if result[0] != '':
c = int(result[0])
code += chr(c)
continue
if 'ROT_TWO' in line and len(code) > 0:
code = code[::-1]
flag += code
code = ''
print flag