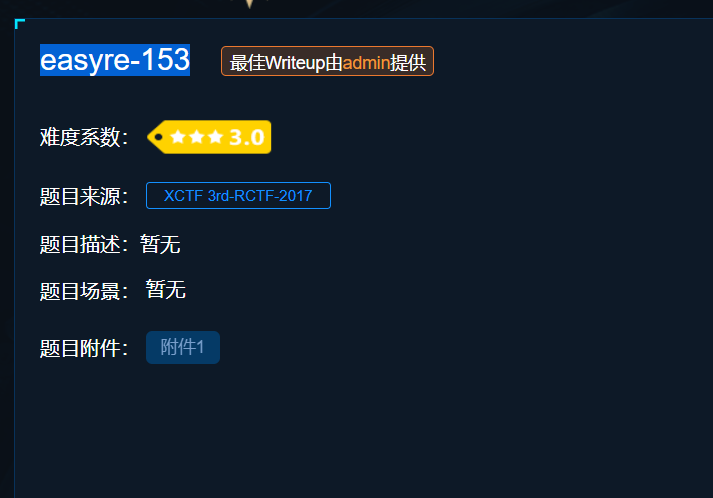
使用detect it easy查壳,upx的壳
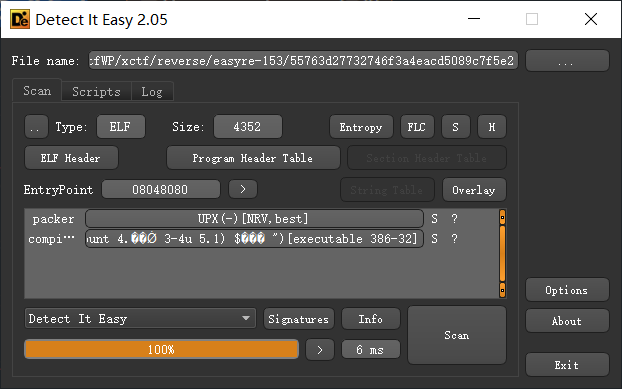
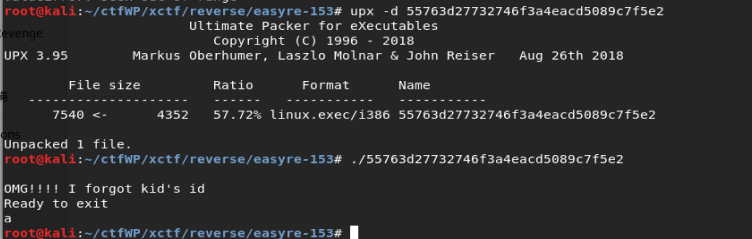
放到kali下脱壳 upx -d filename,脱壳后可以执行了,之前不可以
使用ida打开
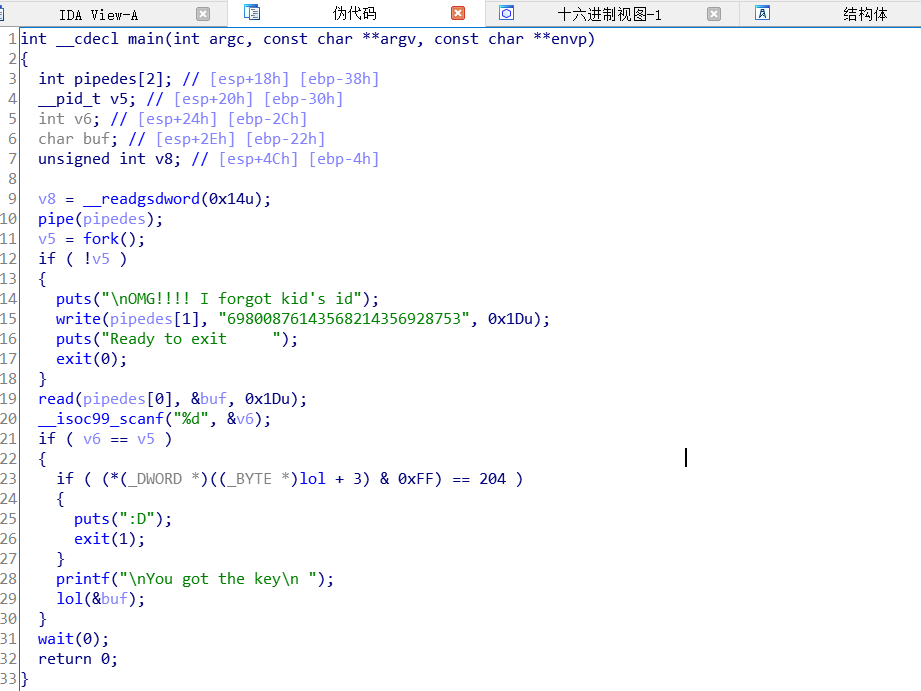
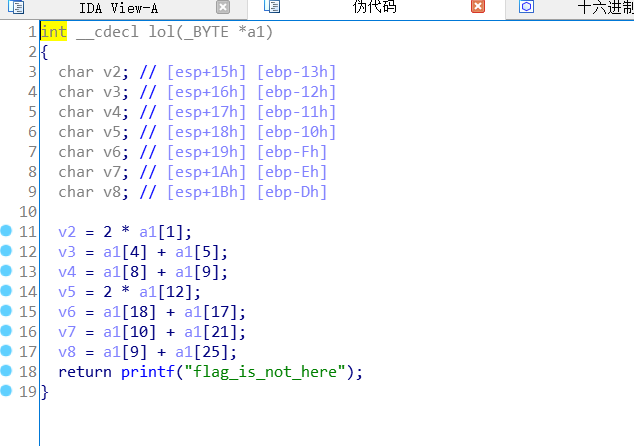
需要注意的事, v2=2*a1[1] = 2* ord(a1[1])
str = '69800876143568214356928753'
a1 = [ord(i) for i in str]
v2 = 2 * a1[1]
v3 = a1[4] + a1[5]
v4 = a1[8] + a1[9]
v5 = 2 * a1[12]
v6 = a1[18] + a1[17]
v7 = a1[10] + a1[21]
v8 = a1[9] + a1[25]
print chr(v2), chr(v3), chr(v4), chr(v5), chr(v6), chr(v7), chr(v8)
#r h e l h e g
#加上RCTF{rhelheg}